Trust the Mobile Authentication Process
Benefits of Mobile Lock
Increased Trust
Easy Deployment
Reduced Risk
Mobile Lock Features
Mobile Lock is the mobile security capability that makes using mobile devices more secure without compromising the user experience.
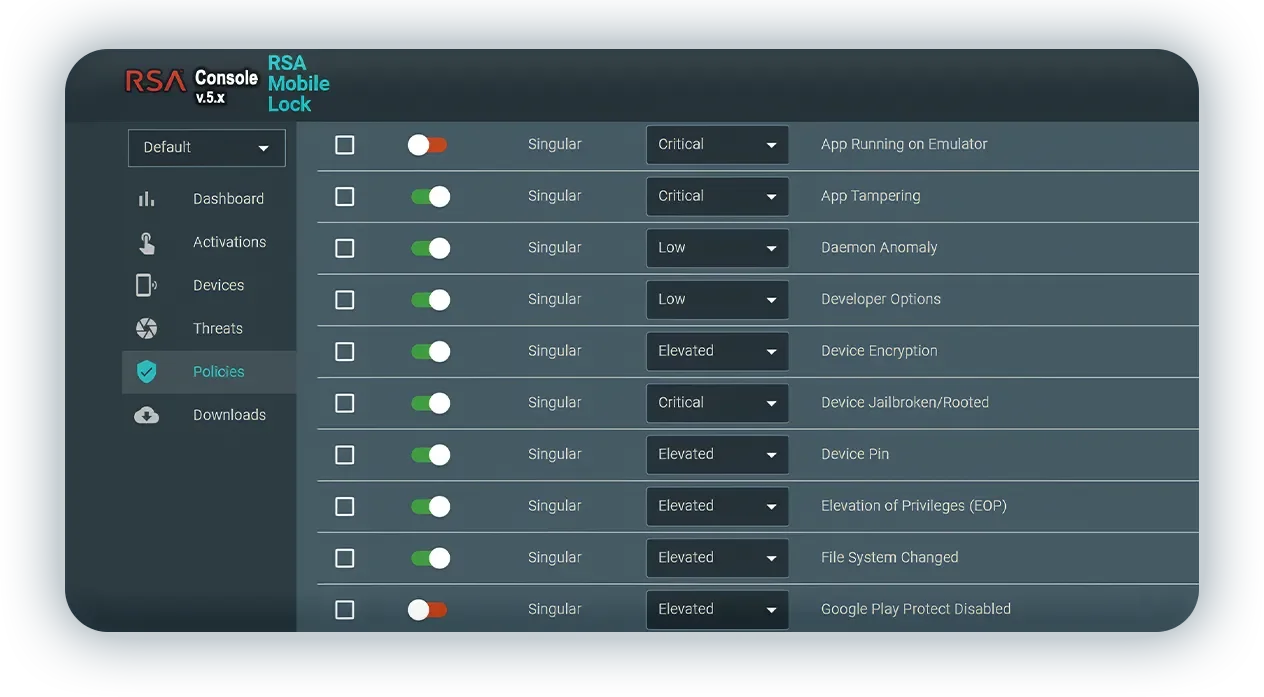
- Easy deployment with pre-configured options out of the box; or configurable based on your specific threat priorities.
- RSA Mobile Lock Console with tools for determining threat details on specific devices to help quickly resolve security threats on that device
- Disables a device’s capability to authenticate into secured environments when a threat is detected
- When a mobile device is “Mobile Locked,” it will retain all other functionality such as text, web browsing, and phone calls.
- Protects the authenticator from over 60 mobile threats.
Specs/Requirements
RSA Mobile Lock identifies security threats on mobile devices and can restrict new authentication requests, thereby securing access to protected resources. This capability enables organizations to establish trust by systematically validating mobile authentication throughout their IT estate while actively identifying threats.
When a user attempts to authenticate, RSA Mobile Lock searches for threats on their mobile device; if a threat is detected, the authentication process is restricted and access to secure environments, including company data, enterprise systems, and customer records, is prevented. This proactive measure effectively contains threats, preventing them from spreading beyond a single compromised device and averting widespread consequences for an organization. Using the Mobile Lock console, organizations can easily customize and prioritize the list of threats they wish to detect and define the appropriate responses.
Given the prevalence of Bring Your Own Device (BYOD) policies today, it’s essential to consider how requirements to enforce corporate security on personal devices can potentially disrupt the user experience. RSA Mobile Lock minimizes this risk by seamlessly integrating into RSA Authenticator for iOS and Android, eliminating the need for a separate installation. Additionally, if Mobile Lock detects a threat, the solution only suspends the user’s ability to use RSA Authenticator, and maintains their ability to make calls, text, browse the internet, and use other device features.
RSA Mobile Lock protects the authentication process and stops mobile devices with security concerns from accessing valuable corporate assets. While not visible to users, Mobile Lock scans the device every time an authentication is attempted.
Part of a Unified Identity Platform
RSA Mobile Lock is part of the AI-powered RSA Unified Identity Platform. The platform combines automated identity intelligence, authentication, access, governance, and lifecycle into one cohesive solution, to protect the gaps and blind spots that result from combining multiple point solutions.

Learn more about Mobile Lock
Better Security for Managed or Unmanaged Devices
RSA Mobile Lock can improve mobile device security in any industry that deploys managed and/or unmanaged mobile devices for users to authenticate. It enables security teams to detect, contain, and respond to a threat, while the user remains free to use the device for other purposes until the threat issue is resolved.